Cloud adoption is (for most cases) a no-brainer and businesses that don't have an IT army will greatly benefit from "owning less" of the IT stack. However, jumping into Cloud on a lark and a credit card is also their Cloud adoption's Achilles' heel.
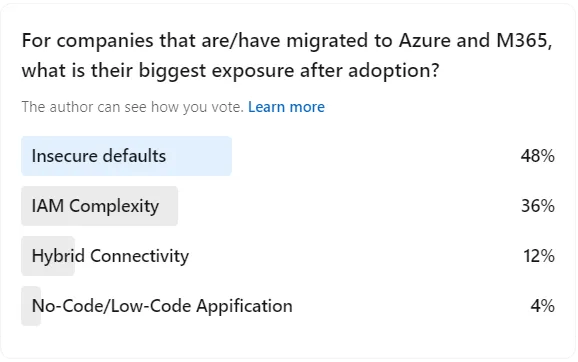
Last week's LinkedIn survey concluded the "Cloud is more secure" dogma's inconvenient truth: only if you let it. When organizations jump into Cloud it is as simple as pulling out the credit card and moving your IT services and workloads at will. However, as the community has pointed out via the survey results below (and I can confirm via incident response lessons learned): insecure defaults of a fresh Cloud deployment and secondarily the complexity of Identity and Access Management can lead to a bad day.
Insecure defaults
This is not to say that spinning up an M365 instance = breach but there are two things I'd like to point out: As per Chris Timmons, older M365 accounts were deployed less secure and exist across the Internet, your company's account may be one of them. And two, as Sandy Buchanan has pointed out, if you have spun up an M365 account more recently it gives you the option to turn on "secure defaults". Aren't defaults on by... Default?
Identity and Access Management (IAM)
"Identity is the new perimeter" is a buzzword but also the truth. As we move away from relying on the network layer for access control and head towards the buzzword land of zero trust, identity and the access control mechanisms behind it will be everything. Considering the future of IAM goes well beyond humans, this will be naturally complex, and without a strategic and modern approach to IAM, Cloud adopters are going to bring their legacy skeletons in the closet with them.
So, is Cloud bad?
Absolutely not. But, companies that have/are moving to the Cloud internally or via a Managed Service Provider (MSP) should recognize there are architecture and configuration considerations to set them up for success.
Is your M365 and/or Azure tenants sitting as default or aligned with industry-leading practices? If not, let's talk about hardening your M365 and Azure environments.

